Detektix Platform
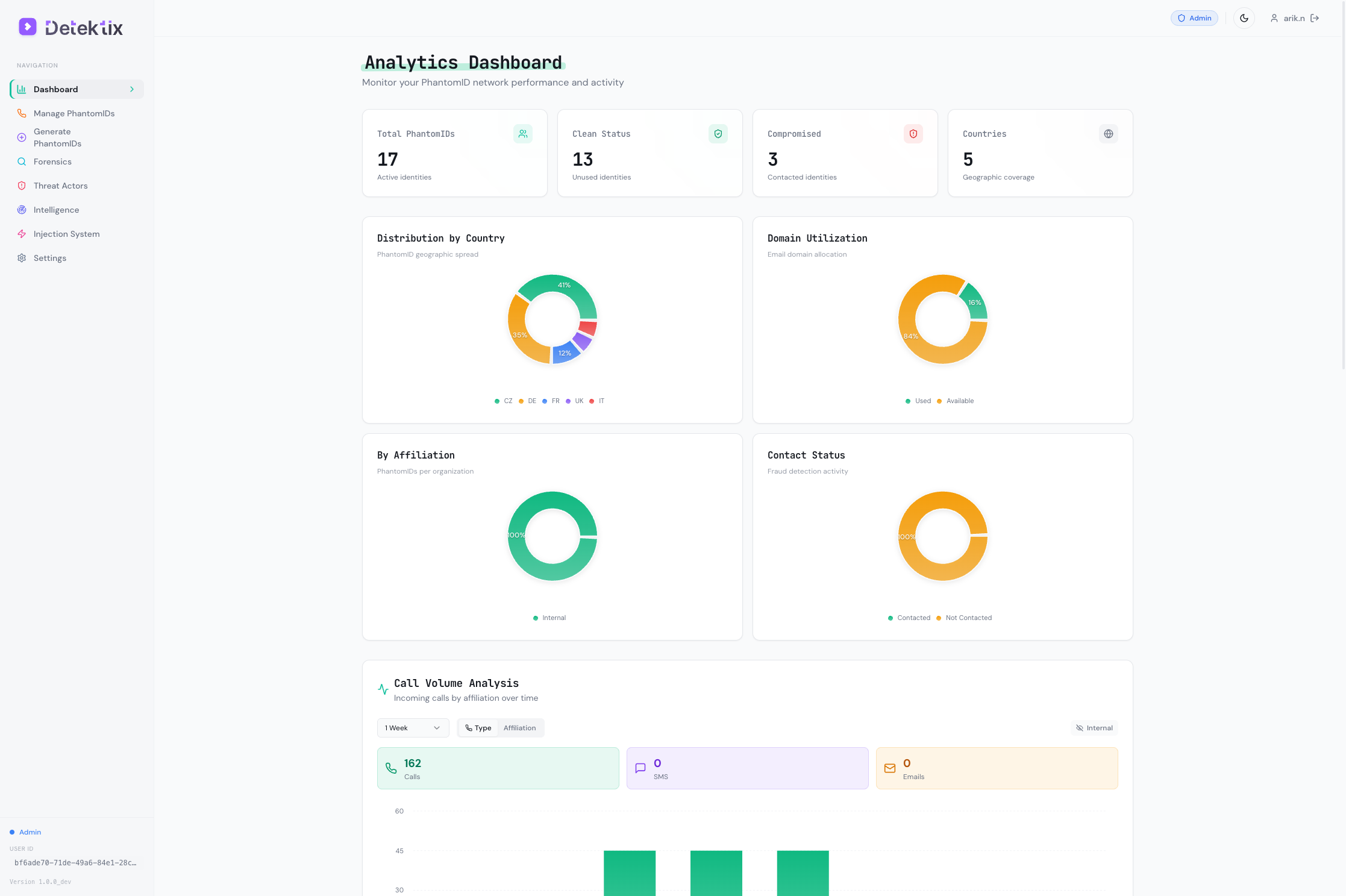
Detektix is a honeypot management and threat intelligence platform that deploys synthetic identities across multiple channels to detect fraud, track data leaks, and identify threat actors targeting your organization.
How It Works
Detektix creates realistic fake identities — complete with phone numbers, email addresses, and registration data — then strategically plants them into platforms where data exposure would indicate a breach. When someone contacts or uses these planted identities, Detektix captures the activity and traces it back to the source.
The PhantomID Lifecycle
| Phase | Description |
|---|---|
| Generate | Create synthetic identities (PhantomIDs) with realistic personal data tailored to your target regions and languages |
| Inject | Deploy PhantomIDs into CRMs, websites, databases, email lists, and other platforms through automated injection |
| Monitor | Track all calls, SMS messages, and emails received by PhantomID phone numbers and email addresses |
| Detect | Identify when planted data is accessed, leaked, or sold — any contact with a PhantomID is a signal |
| Investigate | Analyze patterns using forensic tools, network graphs, and threat actor profiling |
| Report | Generate intelligence reports, manage incidents, and track remediation |
Core Capabilities
PhantomID Management
Generate and manage synthetic identities at scale. Each PhantomID includes a name, email address, phone number, physical address, and metadata — all realistic and region-appropriate. Organize them by affiliation (business unit), tag them for categorization, and track their lifecycle status.
Multi-Channel Injection
Deploy PhantomIDs into external platforms through a flexible injection system:
| Channel | How It Works |
|---|---|
| REST APIs | Direct API calls to CRMs and platforms (Salesforce, HubSpot, etc.) |
| Web Forms | AI-powered browser automation that fills registration forms |
| CRM Platforms | Native integrations with Zendesk and other CRM systems |
| Communication Tools | Slack channel uploads and messaging |
| Databases | Direct insertion into target databases |
| Cloud Storage | File uploads to S3 and similar services |
Forensics & Detection
When a PhantomID receives a call, SMS, or email, the platform captures:
- Call details — Caller ID, duration, recording, direction, timestamp
- SMS content — Message body, sender, media attachments
- Email data — Sender, subject, body, attachments, headers
All communications are visualized in an interactive network graph that maps relationships between threat actors, PhantomIDs, and communication channels.
Threat Intelligence
The platform automatically detects threat actors by analyzing patterns:
- Phone numbers that call multiple PhantomIDs
- Email addresses that contact planted identities
- SMS senders targeting your honeypots
- Cross-channel patterns linking different attack vectors
Each threat actor gets a profile with threat level classification, contact history, source attribution, and an activity timeline.
Campaigns & Incident Management
Organize your PhantomID deployments into campaigns with defined objectives and timelines. When suspicious activity is detected, the system creates incidents with severity levels and a structured response workflow:
New → Acknowledged → Investigating → Confirmed → Remediated → Closed
AI-Powered Voice
PhantomID phone numbers can be backed by AI voice agents that answer calls naturally, engage with callers, and generate transcripts — providing deeper intelligence about who is calling and why.
Key Concepts
PhantomID
A synthetic identity created by the platform. Includes a name, email, phone number, address, and metadata. PhantomIDs are your "canaries" — planted where data exposure would indicate a breach.
Affiliation
An organizational unit (department, brand, region) that owns a group of PhantomIDs. Affiliations provide data isolation, separate analytics, and scoped user access within your tenant.
Injection Target
An external platform where PhantomIDs are deployed. Each target has a type (API, web form, CRM, etc.), configuration, and tracking for success/failure rates.
Threat Actor
An identified entity (person, group, or automated system) that has contacted one or more PhantomIDs. Threat actors are detected automatically or created manually, and tracked with threat levels from Low to Critical.
Campaign
An organized deployment of PhantomIDs to specific injection targets with a defined objective and timeline. Campaigns group related injection activity for tracking and reporting.
Incident
A security event triggered when a PhantomID is contacted. Incidents have severity levels, are linked to threat actors, and follow a structured response workflow.
Platform Architecture
Detektix is built as a multi-tenant SaaS platform with complete data isolation between organizations:
- Isolated database per tenant — your data never shares storage with other organizations
- Dedicated deployment — each tenant has its own application instance
- Shared communication infrastructure — phone numbers and AI voice services are provisioned from shared pools but strictly filtered by tenant
- Role-based access control — three permission levels (Tenant Admin, Admin, Read Only) control what users can see and do
For details on security controls, see Security & Compliance.
Supported Regions & Languages
PhantomID generation supports 40+ locales including:
- English (US, UK, AU)
- German, Austrian German
- Italian, French, Spanish, Portuguese
- Polish, Czech, Romanian, Hungarian
- Japanese, Chinese, Korean
- Arabic, Hebrew, Turkish
- And many more
PhantomIDs are generated with region-appropriate names, addresses, phone formats, and currency settings.